Solana's recent launch of Confidential Balances Token Extensions on mainnet has redefined privacy in high-throughput blockchains, powering the first zero-knowledge encrypted token standard tailored for institutional compliance. With Binance-Peg SOL trading at $82.76 after a 24-hour dip of $1.05 (-0.0125%), the network's sub-second finality and low fees make it ideal for confidential transactions Solana DeFi demands. Developers can now implement encrypted smart contracts Solana that shield balances, enable private transfers, and support auditing, all while preserving liquidity on a permissionless chain. This isn't just incremental; it's a leap toward scalable, privacy-preserving DeFi without the overhead of Layer 2 rollups.
Solana Token-2022: Enabling Encrypted Balances and ZK Proofs
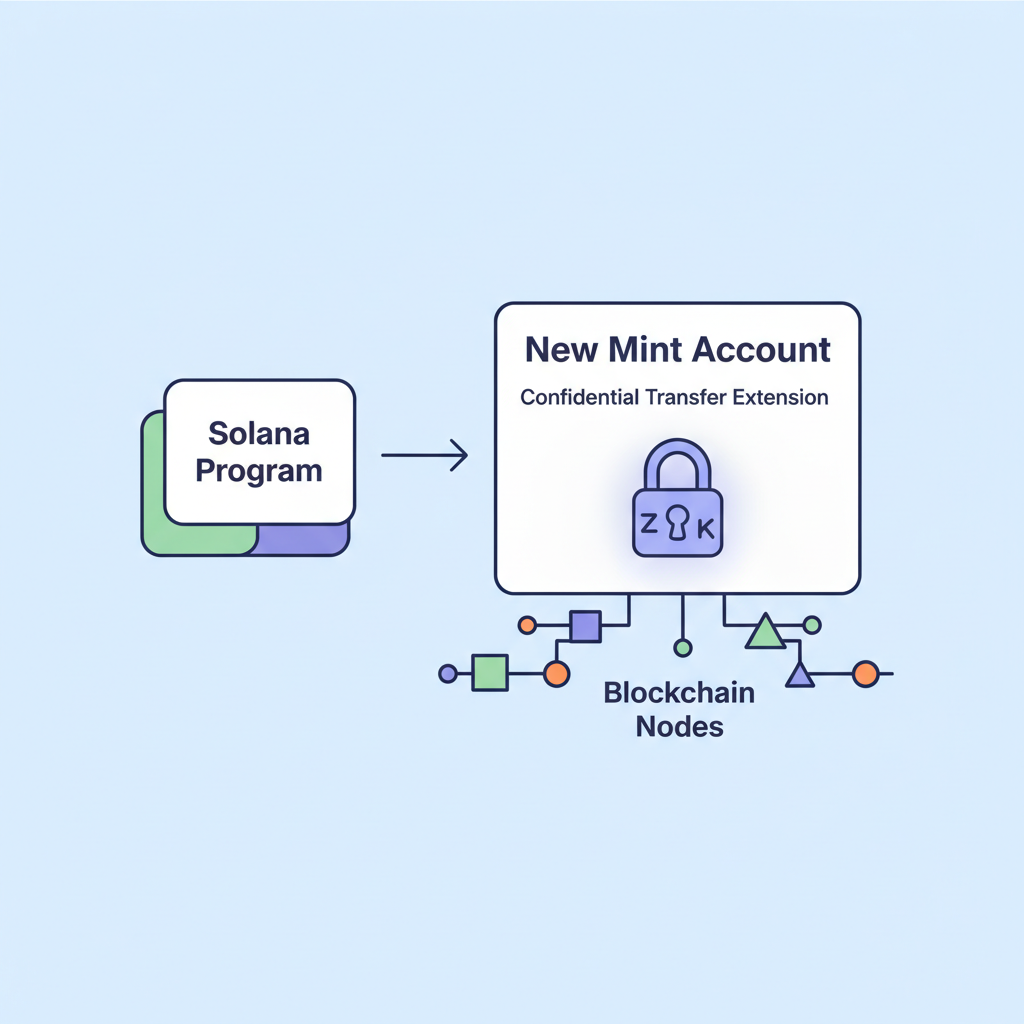
At the core of ZK proof smart contracts Solana lies the Token-2022 program, an evolution of SPL tokens with extensions for confidentiality. Unlike transparent UTXO models or account-based ledgers exposing every balance, Token-2022 encrypts token amounts using ElGamal encryption, paired with zero-knowledge proofs to validate transfers without revealing details. A mint account activates the confidential transfer extension, then associated token accounts store encrypted balances. Pending balances track incoming funds during multi-step proofs, ensuring atomicity.

This setup addresses DeFi's transparency pitfalls, where front-running and MEV drain value. Institutional players, eyeing Solana for payroll or merchant payments, gain configurable privacy: auditors decrypt via authorized keys, regulators verify compliance proofs on-chain. Solana's VM verifies these ZK proofs natively, sidestepping EVM's gas bloat. From my vantage in privacy-focused investments, this native integration outpaces rivals like Ethereum's zk-SNARKs add-ons, delivering verifiable secrecy at scale.
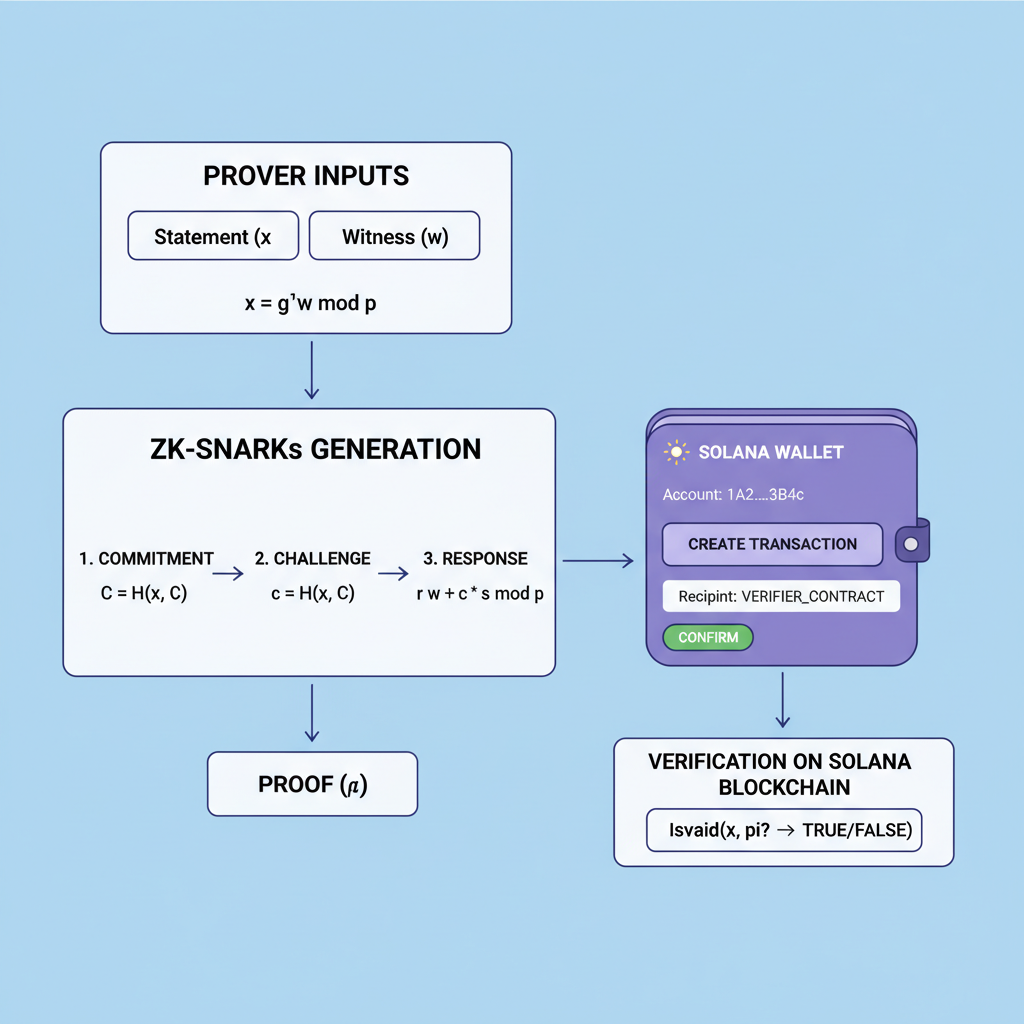
ZK-Proof Fundamentals for Privacy-Preserving Smart Contracts
Zero-knowledge proofs let a prover convince a verifier of a statement's truth without disclosing underlying data. In Solana's context, Bulletproofs and and or similar succinct proofs confirm transfer validity: equality of spent and received amounts, no double-spends, and balance non-negativity. The Fiat-Shamir heuristic transforms interactive proofs into non-interactive ones, hashed into Solana's transaction context for verification.
Projects like Elusiv pioneer this, abstracting ZK shielding for developers. Users deposit to a shared pool, generate proofs for private withdrawals, maintaining fungibility. For smart contracts, integrate via Anchor or native Rust: invoke token program's CPI with proof data. Security hinges on correct transcript mapping; recent audits flagged hash input gaps in sigma protocols, underscoring rigorous spec-to-code fidelity.
Initial Setup: From Mint Creation to Confidential Token Accounts
Implementing Solana encrypted contracts tutorial begins with CLI tools. Install the Solana toolchain, then create a keypair and airdrop SOL for fees. The workflow demands precision: mismatched extensions lead to failed proofs.
SPL Token CLI Commands: Creating and Configuring a Confidential Mint and Token Account
To implement confidential DeFi transactions on Solana, begin by creating a mint with the Confidential Transfer extension using the SPL Token CLI and the Token-2022 program. This extension leverages zero-knowledge proofs for balance privacy. Followed by provisioning and configuring a token account. Ensure your Solana CLI is set to the appropriate cluster (e.g., `solana config set --url devnet`) and your wallet holds sufficient SOL for transaction fees.
# Create a confidential mint with Token-2022 program
# Note the mint address from the output
spl-token create-token \
--program-id TokenzQdBNbLqP5VEhdkAS6EPFLC1PHnBqCXEpPxuEb \
--enable-confidential-transfers \
--decimals 9
# Replace MINT_PUBKEY with the actual mint public key
MINT_PUBKEY=<MINT_PUBKEY>
# Create a token account for the confidential mint
# Note the token account address from the output
spl-token create-account $MINT_PUBKEY
# Replace TOKEN_ACCOUNT with the actual token account public key
TOKEN_ACCOUNT=<TOKEN_ACCOUNT>
# Configure the token account for confidential transfers
spl-token confidential-transfer configure-account $TOKEN_ACCOUNTUpon execution, capture the public keys output by each `create` command to substitute the placeholders. The token account is now ready for confidential deposits, transfers, and withdrawals, forming the basis for ZK-proof encrypted smart contracts in DeFi applications.
First, initialize the mint: spl-token create-token --program-id TokenzQdBNbLqP5VEhdkAS6EPFLC1PHnBqCXEpPxuEb --enable-confidential-transfers. Derive associated accounts with encryption keys. For transfers, clients compute proofs off-chain, submitting proof and ciphertext to the program. Smart contracts then CPI to validate, decrypting only for authorized views.
This foundation empowers DeFi primitives: confidential swaps preserving price impact, yield farms with hidden positions. As SOL holds at $82.76 amid market volatility, builders prioritizing privacy position for institutional inflows, blending speed with secrecy in ways legacy chains envy.
Builders can extend this base into full-fledged ZK proof smart contracts Solana by crafting custom programs that invoke Token-2022's confidential transfer instructions via cross-program invocations (CPI). Imagine a DEX where orders match without exposing sizes or prices; ZK proofs attest to sufficient liquidity and fair execution, all on-chain. This isn't theoretical; protocols like Elusiv and winners from Solana's Privacy Hack bounty demonstrate viable paths, processing millions in private volume while dodging regulatory blind spots.
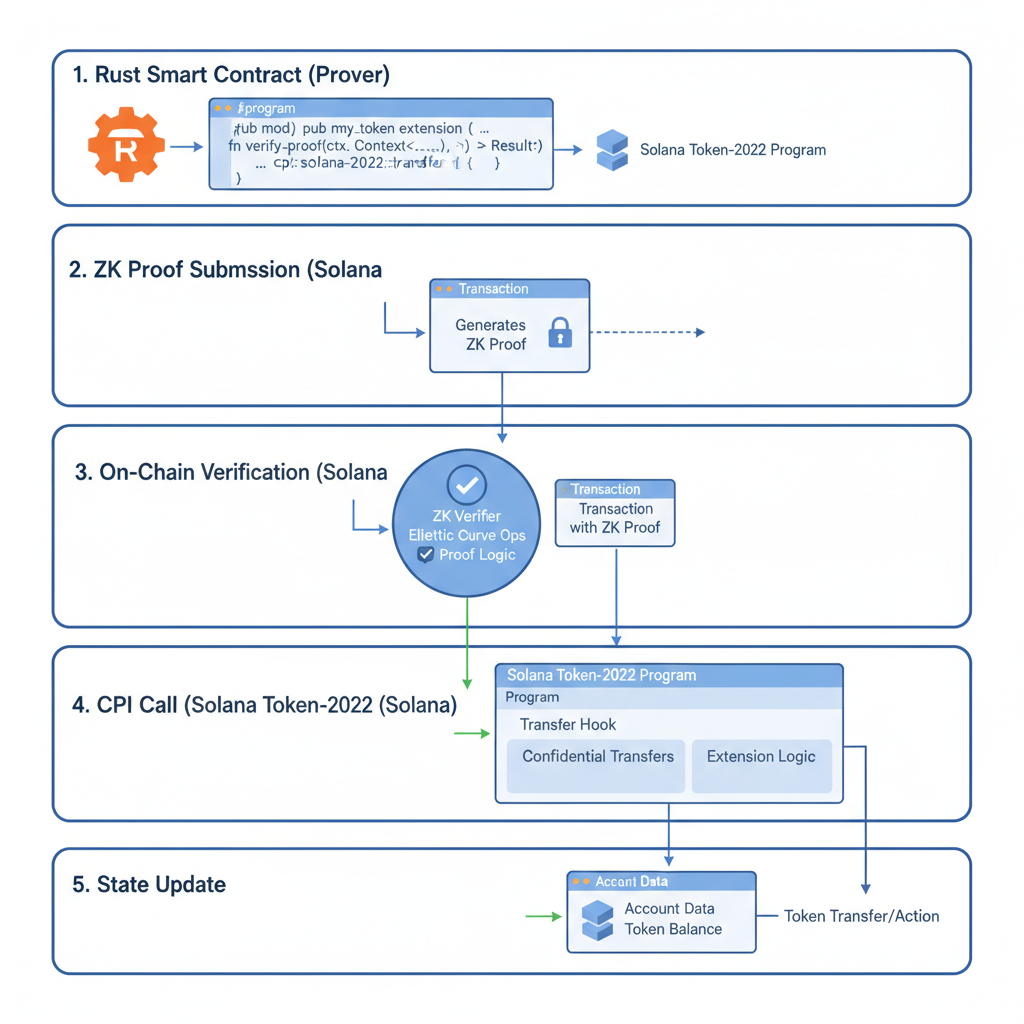
Executing Transfers: ZK Proof Generation and On-Chain Validation
Private transfers demand off-chain proof computation to keep Solana lean. Clients use libraries like spl-confidential-token-ui to generate ElGamal ciphertexts and Bulletproofs for equality and range proofs. Submit these alongside the transaction: the token program decrypts pending balances, applies the proof, and updates accounts atomically. Failure modes, like invalid sigma OR proofs from hash mismatches, highlight the need for audited libraries; cross-reference specs rigorously to avoid exploits.
Confidential Token Transfer CPI with ZK Proof Validation
This Anchor Rust program demonstrates a Cross-Program Invocation (CPI) for a confidential token transfer on Solana. The function validates a zero-knowledge proof to confirm the transfer's correctness—such as sufficient balance and correct amount—without exposing sensitive data. Only upon verification does it invoke the SPL Token program's transfer instruction.
```rust
use anchor_lang::prelude::*;
use anchor_lang::system_program;
use anchor_spl::token::{self, Token, TokenAccount, Transfer};
#[derive(Accounts)]
pub struct ConfidentialTransfer<'info> {
#[account(mut)]
pub from_vault: Account<'info, TokenAccount>,
#[account(mut)]
pub to_vault: Account<'info, TokenAccount>,
/// CHECK: Verified by the ZK proof
pub proof_account: AccountInfo<'info>,
pub token_program: Program<'info, Token>,
pub authority: Signer<'info>,
}
pub fn execute_confidential_transfer(
ctx: Context,
encrypted_amount: Vec,
proof: Vec,
) -> Result<()> {
// Step 1: Validate ZK proof for confidential transfer
// This ensures the transfer is valid without revealing balances or amounts
require_keys_eq!(
ctx.accounts.proof_account.key(),
&expected_proof_pda(&ctx.accounts.from_vault.key(), &ctx.accounts.to_vault.key())?,
CustomError::InvalidProofAccount
);
// Placeholder for on-chain ZK verification (e.g., using Groth16 or custom verifier)
require!(
zk_verify_transfer_proof(&proof, &encrypted_amount, ctx.accounts.from_vault.key(), ctx.accounts.to_vault.key())?,
CustomError::InvalidProof
);
// Step 2: Decrypt or handle confidential amount (simplified; real impl uses homomorphic ops or commitments)
let amount = decrypt_amount(&encrypted_amount, &ctx.accounts.authority)?;
// Step 3: CPI to SPL Token program for the actual transfer
let cpi_accounts = Transfer {
from: ctx.accounts.from_vault.to_account_info(),
to: ctx.accounts.to_vault.to_account_info(),
authority: ctx.accounts.authority.to_account_info(),
};
let cpi_program = ctx.accounts.token_program.to_account_info();
let cpi_ctx = CpiContext::new(cpi_program, cpi_accounts);
token::transfer(cpi_ctx, amount)?;
Ok(())
}
// Placeholder functions for illustration
fn zk_verify_transfer_proof(_proof: &[u8], _enc_amount: &[u8], _from: Pubkey, _to: Pubkey) -> Result<()> {
// Integrate with Solana-compatible ZK verifier (e.g., light-protocol or custom)
Ok(())
}
fn decrypt_amount(_enc: &[u8], _auth: &Pubkey) -> Result {
// Use threshold decryption or similar in production
Ok(0)
}
#[error_code]
pub enum CustomError {
#[msg("Invalid ZK proof")]
InvalidProof,
#[msg("Invalid proof account")]
InvalidProofAccount,
}
``` Key analytical points: (1) ZK proof validation occurs on-chain using a verifier circuit tailored for Solana's compute limits; (2) Encrypted amounts maintain confidentiality via homomorphic encryption or Pedersen commitments; (3) Real-world integrations would leverage libraries like Light Protocol or zk-SNARKs from the Solana Program Library. This ensures privacy-preserving DeFi transactions while upholding Solana's performance.
In practice, this yields sub-second private swaps at fractions of a cent. For DeFi, layer on homomorphic commitments: lenders prove solvency without revealing positions, borrowers hide utilization ratios. My portfolio experience underscores the edge; privacy mitigates liquidation cascades in volatile markets, where SOL's $82.76 stability amid a -0.0125% dip signals resilience for such innovations.
Advanced DeFi Applications: From Payroll to Auditable Yield
Confidential transactions Solana DeFi unlock payroll systems where salaries encrypt end-to-end, minting burns for tax proofs via selective disclosure. Merchant apps process payments invisibly to competitors, while auditors wield view keys for compliance. Yield protocols aggregate hidden stakes, distributing rewards proportionally through ZK-multiples. Arcium's Privacy 2.0 vision amplifies this, offloading heavy ZK to specialized hardware, though Token-2022 suffices for most today.
Institutions, per Taurus SA's review, favor zkOS-like shielding verified by Solana's VM. This beats EVM hacks; no gas wars, pure parallelism. At $82.76, SOL incentivizes deployment now, capturing liquidity before broader adoption spikes fees.
Security and Compliance: Essential Safeguards for Production
Rigorous diligence separates viable projects from rugs. ZK's soundness relies on curve security (Ed25519 resists known attacks), but implementation slips abound: Fiat-Shamir transcripts must chain precisely, per DEV Community audits. Testnets expose edge cases; mainnet demands formal verification where possible.
Compliance toggles privacy: embed KYC proofs or freeze authorities for regulators. This duality courts institutions without alienating cypherpunks. From 14 years assessing risks, I rate Solana's Confidential Balances highest for blending auditability with opacity; rivals lag in native speed.
ZK-powered encrypted smart contracts Solana herald DeFi's mature phase, where privacy fuels growth sans surveillance. With tooling maturing and SOL steady at $82.76 (24h low $80.24, high $83.81), developers hold the keys to institutional trillions. Dive in, verify proofs meticulously, and build the confidential future Solana promises.







No comments yet. Be the first to share your thoughts!