In the shifting sands of 2026 blockchain landscape, developers face a pressing reality: quantum computers loom closer, threatening the cryptographic foundations of EVM-compatible chains. Traditional elliptic curve signatures, once ironclad, now carry latent vulnerabilities that could unravel encrypted smart contracts EVM ecosystems overnight. Yet, proactive platforms like QRL’s Project Zond and QANplatform’s testnet offer a beacon, blending quantum-resistant algorithms with familiar Solidity tooling to safeguard quantum resistant smart contracts without sacrificing usability.
The Quantum Shadow Over EVM Blockchains
Public-key cryptography underpins every transaction and contract deployment on EVM blockchains, from Ethereum Layer 2s to enterprise hybrids. Algorithms like ECDSA and EdDSA excel in speed and compactness but falter against Shor’s algorithm, which could derive private keys from public ones in polynomial time. Hash functions like SHA-256 hold firmer, resisting Grover’s algorithm with doubled key lengths, yet the risk compounds in multi-signature schemes and long-term data storage central to blockchain privacy 2026.
Starknet’s STARK proofs stand out here, inherently quantum-resistant due to their hash-based construction, powering scalable Layer 2s without classical signature dependencies. StarkWare’s CEO Eli Ben-Sasson has championed a five-step roadmap: assess threats, prototype algorithms, test migrations, coordinate ecosystems, and deploy hard forks. This methodical approach resonates with risk managers like myself, who view quantum threats not as distant sci-fi but as foreseeable risks demanding layered defenses.
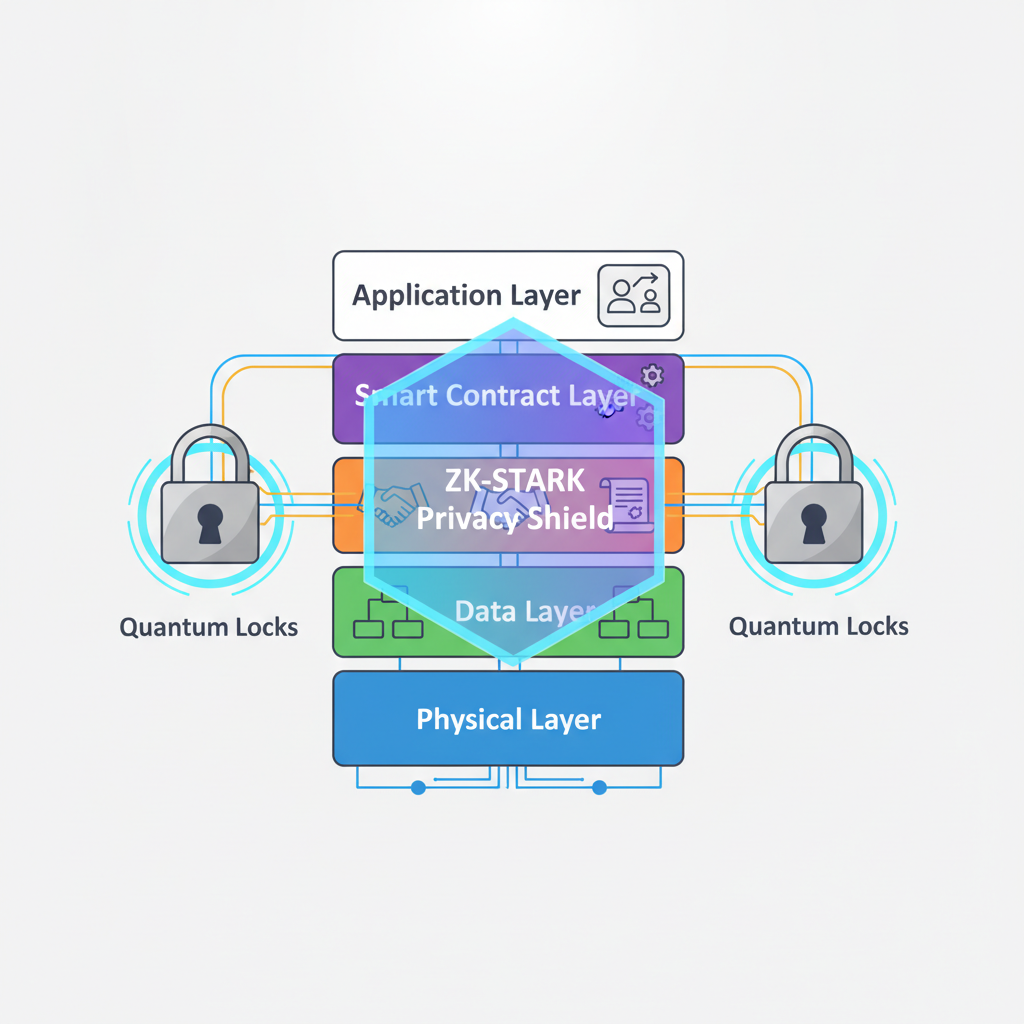
Layer 2 solutions amplify the urgency. zk-STARKs enable zk-STARKs smart contracts that prove computations confidentially, sidestepping quantum-vulnerable signatures entirely. Yet for full EVM compatibility, chains must retrofit post-quantum signatures without bloating gas costs or fragmenting liquidity.
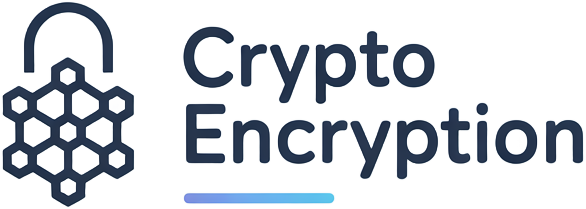
Pioneering Platforms: QRL, QANplatform, and Algorand Lead the Charge
QRL 2.0, dubbed Project Zond, marks a pivotal shift in March 2026 with its EVM-compatible testnet. Swapping XMSS for NIST-approved ML-DSA-87 (Dilithium), it secures state transitions and contract executions against quantum harvest-now-decrypt-later attacks. Developers port Ethereum dApps seamlessly, retaining Web3 wallets and tools while inheriting quantum safety. This aligns with my mantra: smart risk fortifies smart contracts.
QANplatform complements this by launching the first quantum-resistant EVM testnet, fusing Dilithium signatures with multi-language support-Solidity, Python, Go. Its hybrid consensus delivers high throughput and energy efficiency, ideal for quantum safe blockchain contracts in DeFi or supply chains. Unlike pure public chains, it bridges private enterprise needs, proving post-quantum tech scales beyond hype.
Algorand bolsters the field with FALCON-1024 integration, another NIST lattice-based scheme optimized for verification speed. Securing state proofs, it maintains Algorand’s pure proof-of-stake velocity, clocking thousands of TPS without quantum compromise. These platforms underscore a truth: EVM compatibility need not dilute security; it amplifies it.
Quantum-Resistant EVM Platforms Comparison
| Platform | Post-Quantum Signature Scheme | EVM Compatibility | Testnet/Status (as of March 2026) | Supported Languages | Key Features |
|---|---|---|---|---|---|
| QRL 2.0 (Project Zond) | Dilithium (ML-DSA-87) | Full EVM compatibility | Testnet launched Q1 2026 | Solidity | Port Ethereum contracts with minimal changes, familiar Web3 tooling |
| QANplatform | Dilithium | Multi-language EVM testnet | Testnet launched (world’s first quantum-resistant EVM testnet) | Solidity, Python, Go | Hybrid public-private chain, energy-efficient consensus, high throughput for enterprises |
| Algorand | FALCON-1024 | State proofs integration (AVM) | Integrated | TEAL (native smart contracts) | High TPS PoS, efficient verification |
Core Cryptographic Primitives for Implementation
Lattice-based schemes dominate 2026 roadmaps. Dilithium (ML-DSA) balances security, signature size around 2.5KB, and verification under 10 microseconds-far slimmer than hash-based XMSS. FALCON shrinks further to 1KB signatures via NTRU lattices, suiting bandwidth-constrained mobile wallets. Both withstand quantum parallelism, with security levels matching AES-128 or higher.
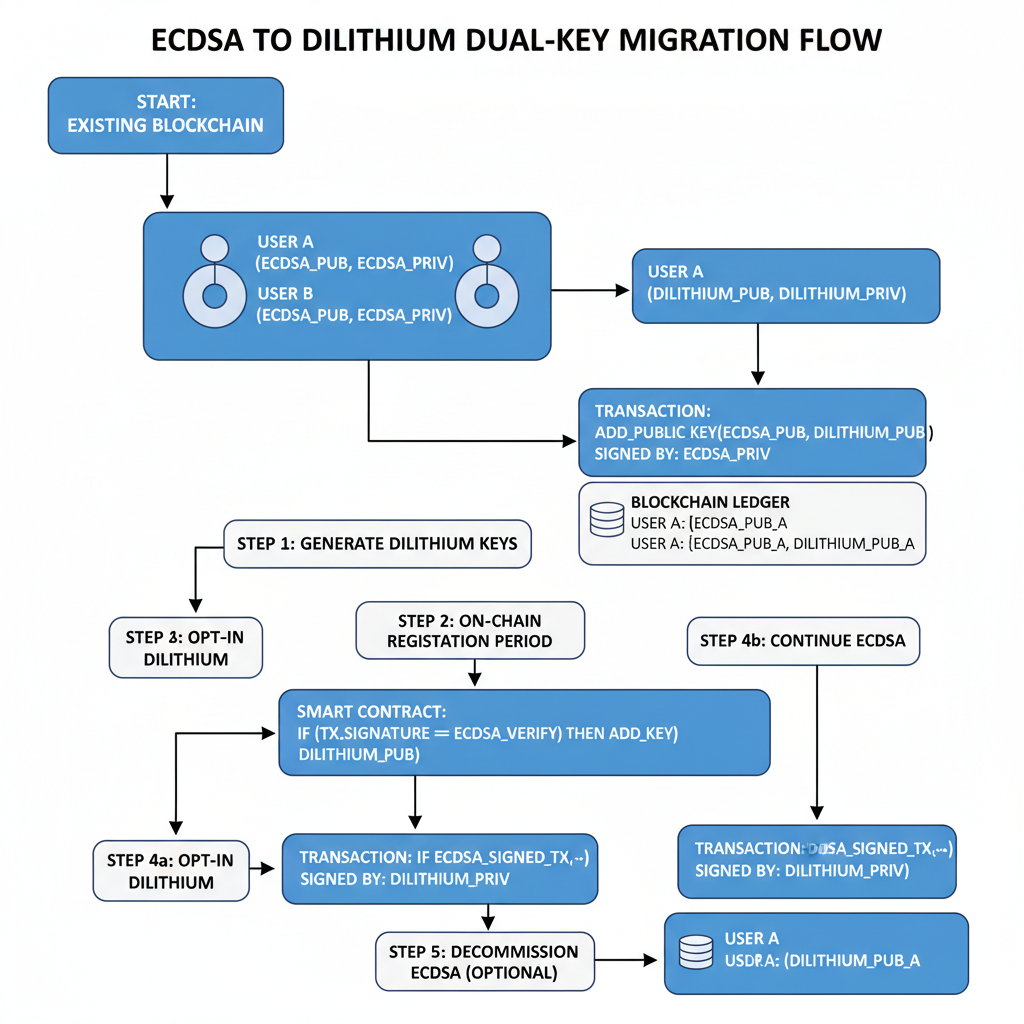
Integrating these into EVM demands precompiles for efficient verification, akin to Ethereum’s secp256k1 opcodes. Contracts must migrate keys gradually-dual-signature periods allow classical fallbacks during transitions. Privacy layers add nuance: FHE or ZK over post-quantum signatures enable fully homomorphic encrypted smart contracts EVM, computing on ciphertexts without decryption.
Hash-based signatures like XMSS offer information-theoretic security but suffer from stateful key usage, limiting reuse in dynamic smart contracts. Developers must weigh trade-offs: lattice schemes prioritize stateless efficiency, while STARKs eliminate signatures altogether in proof systems. My experience in risk management favors hybrid approaches, layering post-quantum primitives atop ZK for quantum safe blockchain contracts that endure both classical and quantum scrutiny.
Step-by-Step Implementation on EVM Chains
Deploying quantum resistant smart contracts starts with chain selection-QRL 2.0 or QANplatform testnets provide ready EVM environments. Begin by auditing dependencies: replace ECDSA with Dilithium precompiles. Ethereum’s opcode extensions, proposed in EIP drafts, enable this via assembly calls, slashing verification costs by 90% over naive implementations.
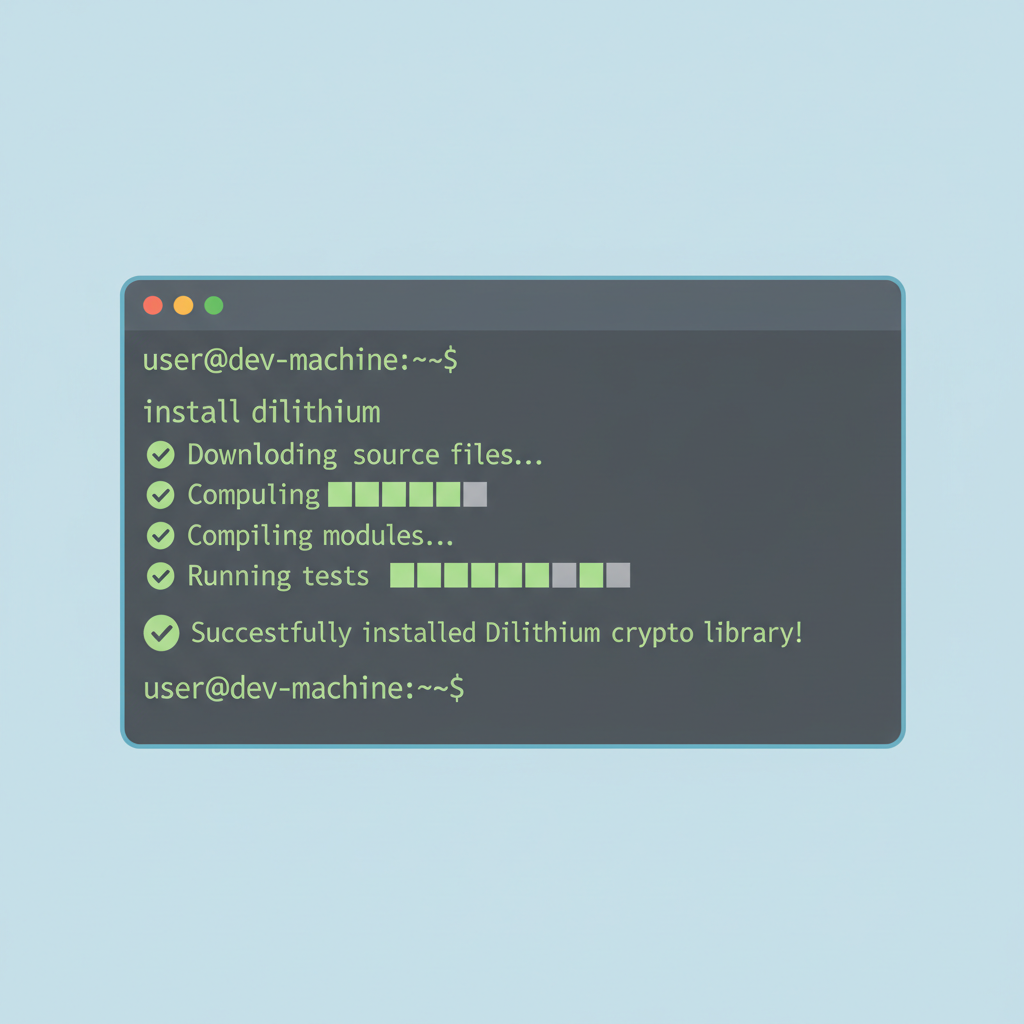
Dilithium Signature Verification Precompile in a Simple Escrow Contract
This Solidity contract provides a practical example of integrating Dilithium signature verification via a precompile in an EVM-compatible quantum-resistant blockchain. The escrow workflow is as follows: the buyer creates an escrow by depositing funds, specifying the seller’s address, a pre-agreed message hash (e.g., signed off-chain over escrow details), and the seller’s Dilithium public key. The seller then calls `releaseFunds` with their signature over the message hash, which is verified on-chain using the precompile at address `0x…4242`.
```solidity
pragma solidity ^0.8.20;
contract QuantumResistantEscrow {
address constant DILITHIUM_PRECOMPILE = address(0x00000000000000000000000000000000004242);
struct Escrow {
address buyer;
address payable seller;
uint256 amount;
bytes32 messageHash;
bytes sellerPublicKey;
bool released;
bool refunded;
}
mapping(uint256 => Escrow) public escrows;
event EscrowCreated(uint256 indexed id, address buyer, address seller, uint256 amount);
event FundsReleased(uint256 indexed id);
event FundsRefunded(uint256 indexed id);
/// @notice Creates a new escrow, depositing funds and specifying seller details
function createEscrow(
uint256 id,
address payable _seller,
bytes32 _messageHash,
bytes calldata _sellerPublicKey
) external payable {
require(escrows[id].buyer == address(0), "Escrow already exists");
require(msg.value > 0, "Must deposit funds");
escrows[id] = Escrow({
buyer: msg.sender,
seller: _seller,
amount: msg.value,
messageHash: _messageHash,
sellerPublicKey: _sellerPublicKey,
released: false,
refunded: false
});
emit EscrowCreated(id, msg.sender, _seller, msg.value);
}
/// @notice Seller releases funds by providing a valid Dilithium signature
function releaseFunds(uint256 id, bytes calldata signature) external {
Escrow storage escrow = escrows[id];
require(msg.sender == escrow.seller, "Only seller can release");
require(!escrow.released && !escrow.refunded, "Escrow already settled");
require(verifyDilithium(escrow.sellerPublicKey, signature, escrow.messageHash), "Invalid Dilithium signature");
escrow.released = true;
escrow.seller.transfer(escrow.amount);
emit FundsReleased(id);
}
/// @notice Buyer refunds funds if not released (simplified, no signature required)
function refund(uint256 id) external {
Escrow storage escrow = escrows[id];
require(msg.sender == escrow.buyer, "Only buyer can refund");
require(!escrow.released && !escrow.refunded, "Escrow already settled");
escrow.refunded = true;
payable(escrow.buyer).transfer(escrow.amount);
emit FundsRefunded(id);
}
/// @notice Verifies Dilithium signature using the chain's precompile
function verifyDilithium(
bytes calldata publicKey,
bytes calldata signature,
bytes32 messageHash
) internal view returns (bool) {
bytes memory inputData = abi.encodePacked(publicKey, signature, messageHash);
(bool success, bytes memory result) = DILITHIUM_PRECOMPILE.staticcall(inputData);
if (!success) {
return false;
}
return abi.decode(result, (bool));
}
}
```The `verifyDilithium` function assumes the precompile expects concatenated input of public key bytes, signature bytes, and 32-byte message hash, returning a boolean. In a real deployment, consult the chain’s specifications for the exact precompile address, input format, gas costs, and Dilithium parameters (e.g., Dilithium2 or Dilithium3). The refund function is simplified here; production versions might require buyer signatures as well.
Next, orchestrate key migration. Dual-mode contracts support both old and new signatures during a sunset period, typically 12-18 months. Node operators upgrade firmware synchronously, as OKX Ventures notes, to avoid fork risks. Testnets like QANplatform’s simulate this, allowing dry runs for DeFi protocols handling billions in TVL.
Incorporate privacy via zk-STARKs for zk-STARKs smart contracts. Starknet’s prover generates succinct, quantum-secure proofs verifiable on EVM, enabling confidential balances or private auctions without exposing inputs. This fusion addresses blockchain privacy 2026 mandates from regulators eyeing MiCA extensions.
Challenges and Risk MitigationsNavigating Gas Bloat and Ecosystem Lock-in
Signature sizes pose the biggest hurdle-Dilithium’s 2.5KB payloads inflate transaction data fivefold over ECDSA’s 70 bytes, spiking gas fees on congested networks. Mitigate with aggregation: BLS-like multi-sig compresses batches, or off-chain relayers handle verification. Algorand sidesteps this via FALCON’s compact 1KB footprints, proving lattice tweaks matter.
Ecosystem coordination lags. Ethereum’s Lean proposal eyes 2027 for PQC, but Layer 2s like Starknet lead with STARKs. Fragmentation risks liquidity splits; bridges must upgrade atomically. In my assessment, projects ignoring Ben-Sasson’s roadmap court obsolescence, as quantum harvest attacks already snag public keys for future decryption.
Performance benchmarks reveal viability. On QANplatform, Dilithium verifies at 200,000 ops/sec, matching classical speeds post-optimization. Energy profiles align with ESG demands, crucial for enterprise adoption in supply chain encrypted smart contracts EVM.
Post-Quantum Signature Benchmarks
| Signature Scheme | Signature Size | Verification Time | Security Level | Notes |
|---|---|---|---|---|
| Dilithium (ML-DSA-87) | 2.5 KB | 8 μs | 128-bit | QRL 2.0 EVM testnet, QANplatform EVM testnet |
| FALCON-1024 | 1 KB | 5 μs | 128-bit | Algorand integration |
| XMSS | 35 KB | 50 μs | Information-theoretic | QRL legacy scheme |
| ECDSA (Baseline) | 70 B | 2 μs | Quantum-vulnerable | Current EVM standard |
Outlook: A Quantum-Proof EVM Ecosystem by 2027
By late 2026, expect mainnet launches-QRL 2.0 eyes Q3, QANplatform Q2-followed by Ethereum L2 forks. Starknet’s BTCFi integrations extend quantum safety to Bitcoin assets, blending STARK scalability with EVM tools via bridges. Algorand’s state proofs secure cross-chain relays, fostering unified liquidity pools.
Developers gain from toolkits: Foundry plugins for PQC testing, Hardhat verifiers simulating Shor attacks. Standards bodies like NIST refine ML-DSA variants, ensuring interoperability. This convergence transforms threats into advantages; quantum-resistant chains attract institutional capital wary of classical risks.
Platforms racing ahead-QRL, QANplatform, StarkWare, Algorand-demonstrate feasibility without reinventing Solidity. For risk-averse builders, the calculus is clear: migrate now to lock in quantum resistant smart contracts, or gamble on grace periods that may never come. Smart risk indeed fortifies the future of blockchain.