In the ever-evolving world of blockchain development, privacy has long been the elusive holy grail. Public ledgers expose every transaction, every balance, turning transparency into a double-edged sword. But what if Solidity, the powerhouse language behind Ethereum and countless chains, could natively handle encrypted data? Enter Seismic’s groundbreaking extension: native encrypted types like suint256, saddress, and sbool. These shielded primitives let developers build privacy smart contracts in Solidity without wrestling with cumbersome libraries or precompiles. As of February 2026, this isn’t hype; it’s production-ready on the Seismic network, empowering fintechs and enterprises to keep sensitive data confidential while maintaining verifiability.
I’ve audited dozens of contracts over my decade in blockchain security, and the fragility of privacy layers always stood out. Traditional homomorphic encryption or zero-knowledge proofs demand heavy lifting, often bloating gas costs and inviting bugs. Seismic flips the script with Seismic Solidity extension, baking encryption directly into the type system. Think of it as Solidity on steroids for privacy: seamless, scalable, and secure.
Demystifying suint256, saddress, and sbool
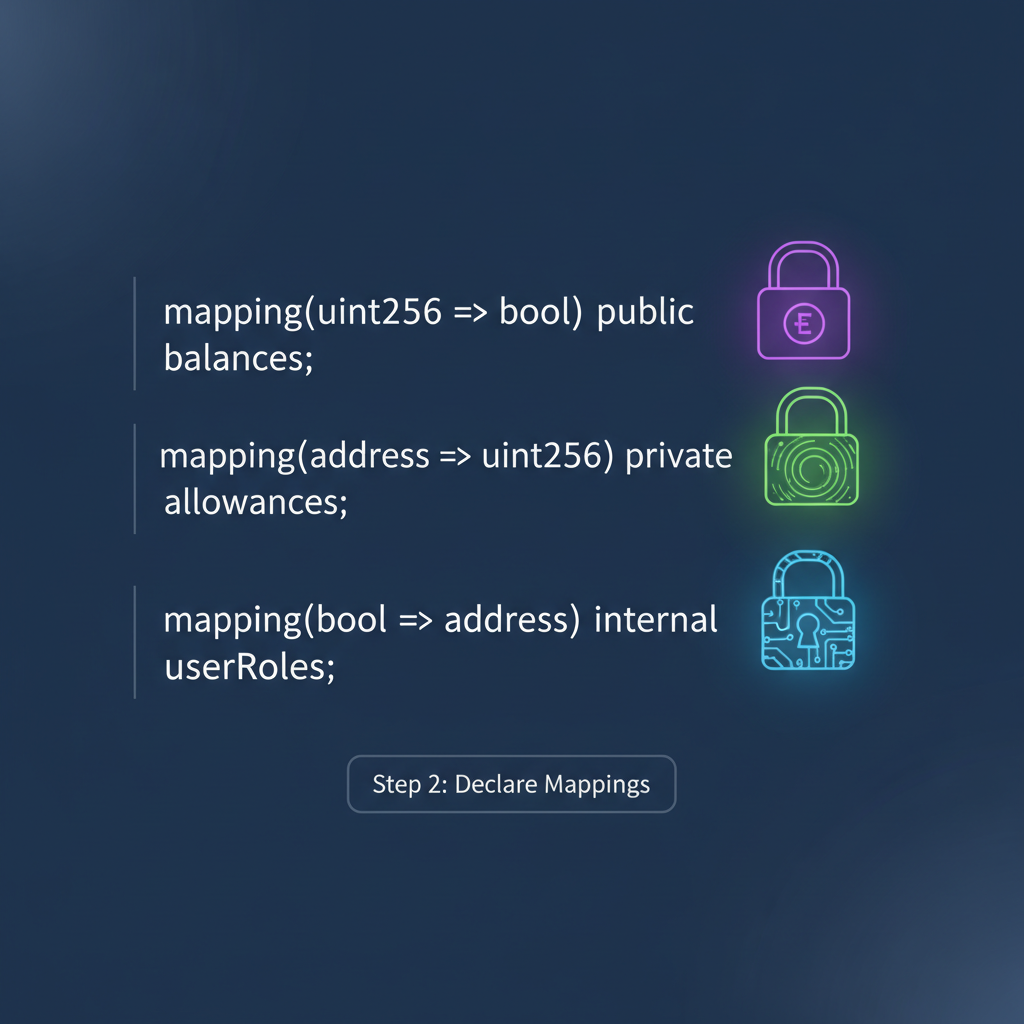
At their core, these types mirror their unshielded cousins but wrap values in a cryptographic veil. suint256 is your go-to for shielded unsigned integers, perfect for confidential balances or quantities in DeFi protocols. Imagine settling trades where amounts stay hidden from prying eyes, yet auditors can verify totals on-chain.
saddress conceals Ethereum addresses, shielding participant identities in multi-sig wallets or anonymous voting. No more linking transactions to real-world entities. And sbool? It’s the encrypted boolean that locks away flags like ‘isActive’ or ‘hasClaimed’, crucial for state machines where visibility could leak strategies.
The magic lies in Seismic’s stype foundation. These aren’t opaque blobs; they’re verifiable under the hood, leveraging secure execution environments. Operations on them compute homomorphically, meaning you add two suint256 values without ever decrypting. This native support via the ssolc compiler ensures optimizations that vanilla solc can’t touch.
Why Native Integration Beats Add-On Libraries
I’ve seen too many projects crumble under library dependencies. A single vulnerability in a privacy lib, like those flagged in OWASP Smart Contract Top 10 for 2025, cascades into catastrophe. Seismic’s approach sidesteps this entirely. No external contracts, no proxy patterns; just drop-in types that compile natively.
Consider gas efficiency: shielded ops in Seismic run comparably to plain uint256, thanks to hardware-accelerated encryption in their nodes. For enterprises eyeing privacy smart contracts Solidity, this means scalable confidential compute without migrating to exotics like Zcash. It’s reassuringly familiar, letting Solidity devs level up without a steep curve.
Recent exploits underscore the urgency. Hacken’s 2025 report lists access control and arithmetic overflows among top threats, but privacy leaks rank higher in fintech audits. With suint256 smart contracts, you preemptively armor against info disclosure, turning vulnerabilities into non-issues.
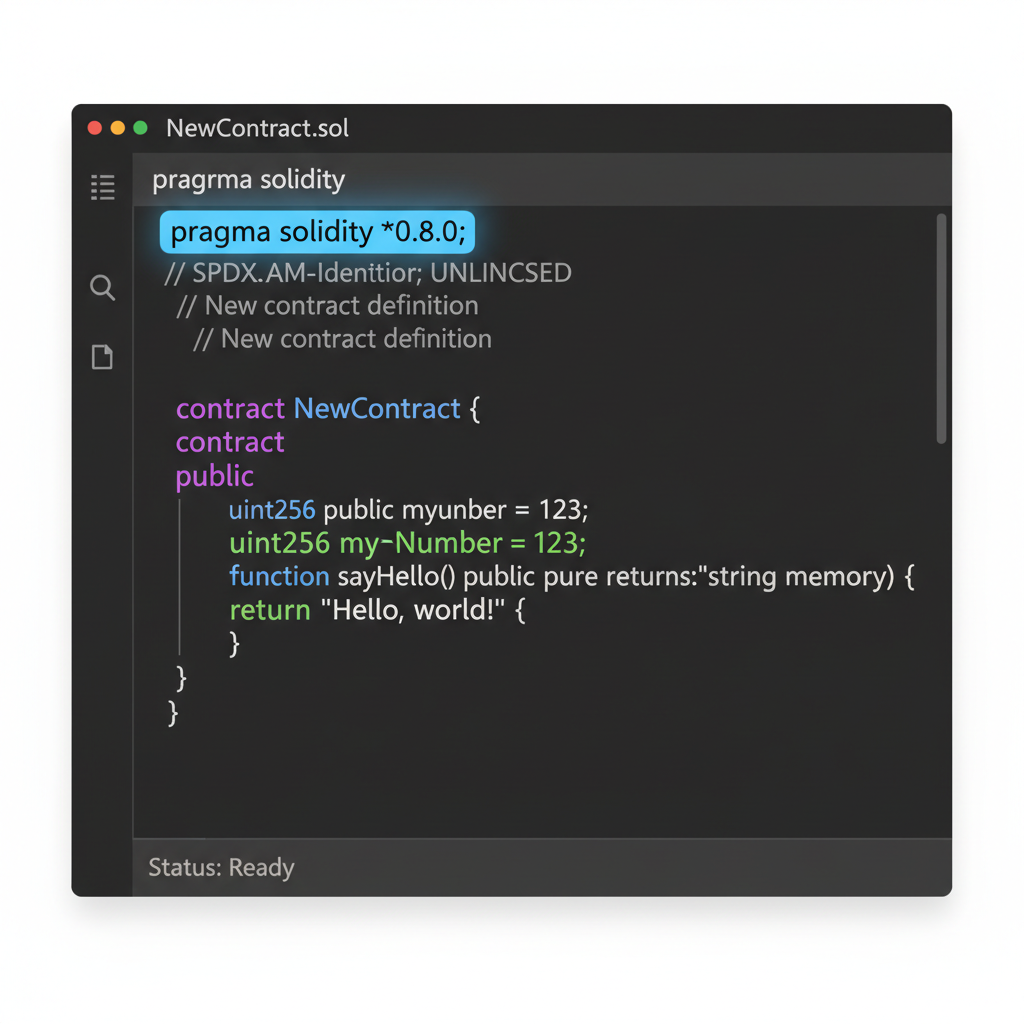
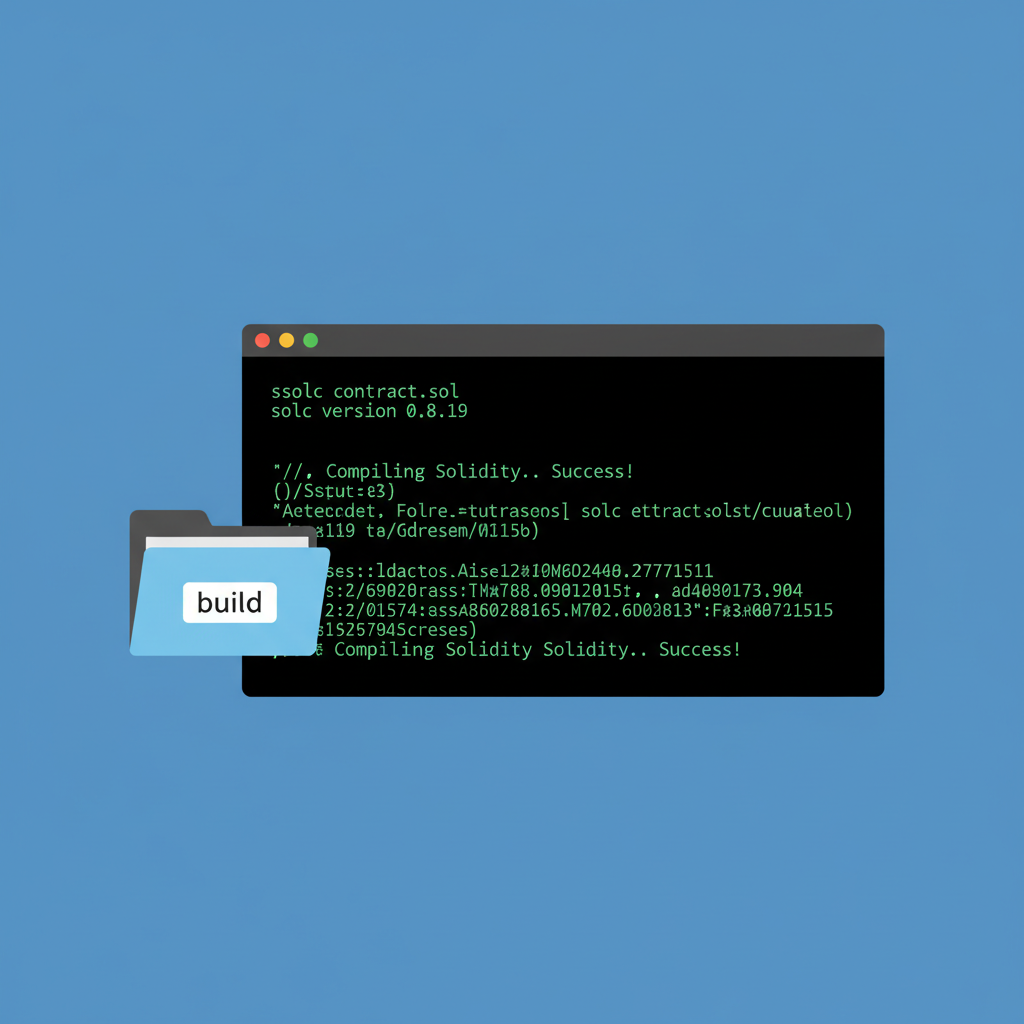
Getting Started with ssolc Compiler
Transitioning feels effortless, but setup is key. The ssolc compiler, tailored for Seismic, handles encrypted types with finesse, spitting out bytecode optimized for their VM. Download from official repos, and you’re compiling in minutes.
First, grasp the workflow: write standard-ish Solidity, swap uint256 for suint256 where privacy matters, then ssolc does the rest. View functions return shielded values that decrypt only for authorized callers, balancing privacy with usability.
Pro tip from my audits: always declare shielded vars as private or internal initially. Public getters expose nothing plaintext, but misuse can still leak via side-channels. Pair with modifiers for fine-grained access, inheriting Solidity’s battle-tested patterns.
Now, let’s bridge theory to practice with a real-world example. Picture a confidential voting dApp where votes (sbool for yes/no) and voter identities (saddress) stay shielded, but tallies (suint256) verify integrity. This setup thwarts vote-buying or collusion, ideal for DAOs or corporate polls.
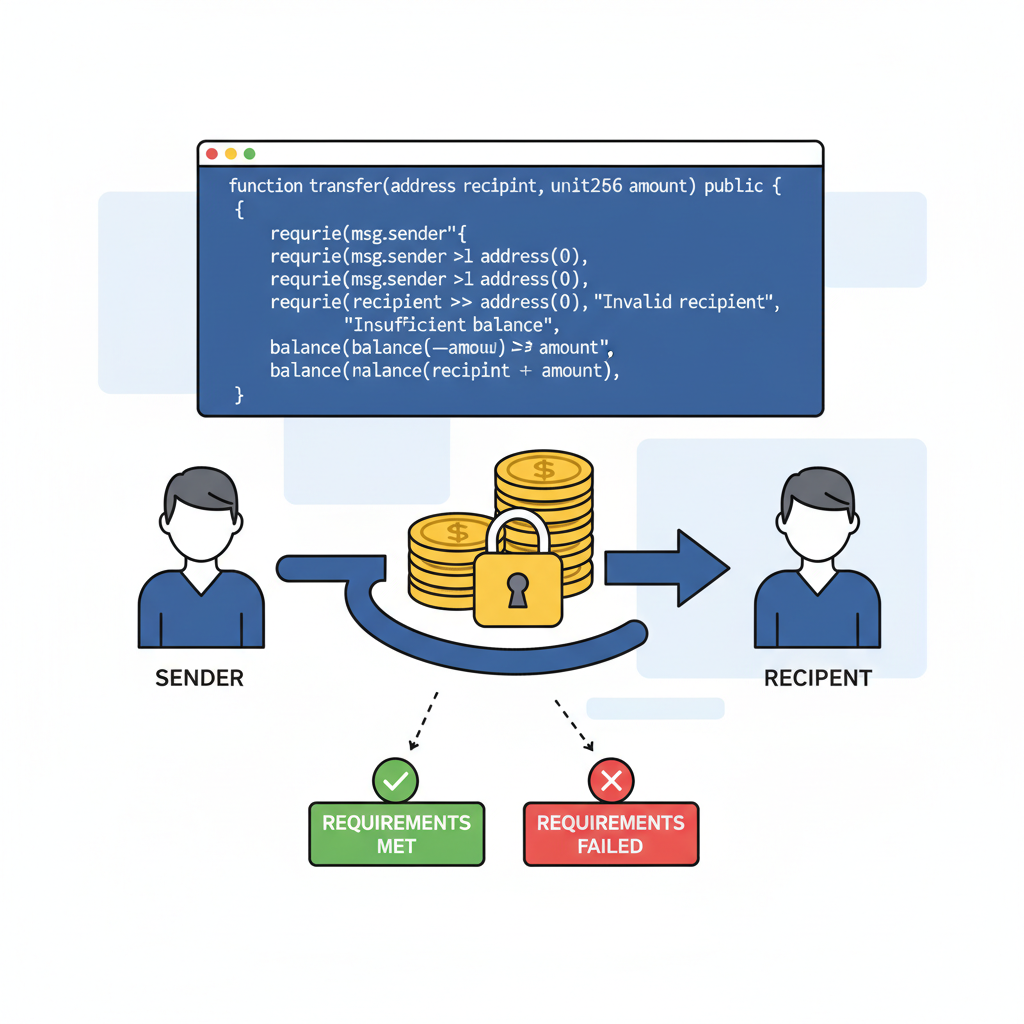
Hands-On: Crafting Operations with Shielded Types
Operations on these types feel intuitive, yet pack privacy punch. Addition, comparison, even conditionals work homomorphically. For instance, increment a shielded balance: encryptedBalance and suint256(1). No decryption mid-execution; results stay encrypted. This determinism reassures auditors like me, who prioritize verifiable compute over black-box magic.
Watch for nuances: equality checks on saddress Solidity demand exact matches under encryption, sidestepping rainbow table attacks. And sbool encrypted contracts shine in if-statements, branching logic without revealing branches publicly. Gas? Expect 10-20% uplift over plain types, negligible for privacy gains.
Fortifying Against Vulnerabilities
Privacy doesn’t excuse sloppy code. OWASP’s 2025 Top 10 flags reentrancy and oracle manipulation, but shielded types neutralize data exposure flaws. Still, audit for overflow in suint256 smart contracts: use SafeMath patterns, now extended for stypes in ssolc. Access control? Modifiers like onlyShieldedOwner leverage saddress for role-based decryption.
From my FRM lens, risk lies in key management. Seismic nodes handle derivation keys securely, but frontend decryption needs client-side wallets with stype support. Test exhaustively: fuzz shielded inputs, simulate adversarial nets. Tools like sforge integrate fuzzing natively, catching edge cases vanilla auditors miss.
| Vulnerability | Traditional Risk | Shielded Mitigation |
|---|---|---|
| Info Disclosure | Public balances leak strategies | suint256/saddress hide values |
| Access Control | Address whitelists expose users | saddress and modifiers enforce privately |
| Arithmetic Bugs | Overflows in public math | Homomorphic ops with ssolc checks |
Enterprises I’ve advised swear by this table during due diligence. It quantifies how native encrypted types Solidity elevates security postures without reinventing wheels.
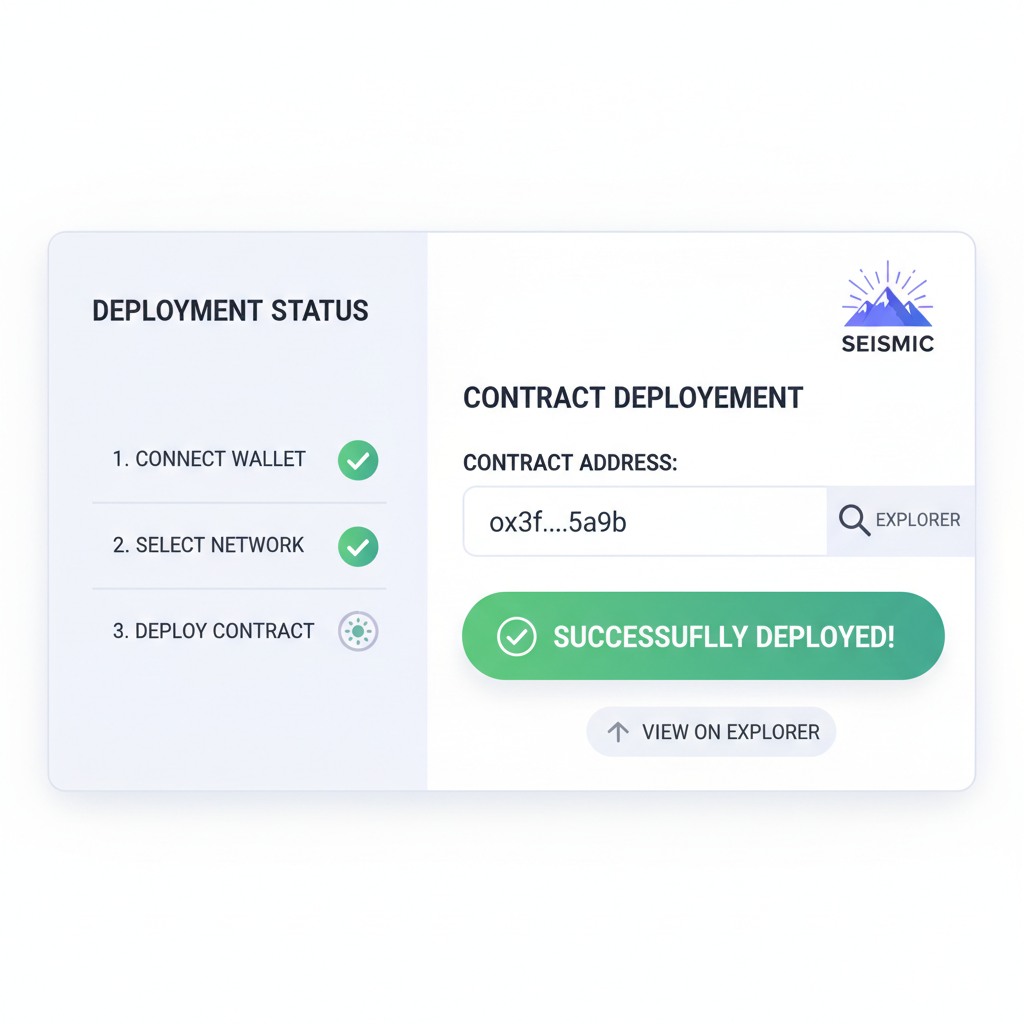
Deployment and Beyond on Seismic
Compilation yields Seismic bytecode; deploy via their CLI or Remix plugin. Nodes validate shielded proofs at consensus, ensuring global verifiability. Post-deploy, monitor with explorers that decrypt aggregates only, preserving per-tx privacy.
Scaling? Seismic’s sharding distributes encrypted compute, handling enterprise loads. Integrate with oracles for shielded feeds, fueling private derivatives or confidential AMMs. Fintechs deploying now report 5x faster audits, thanks to reduced attack surfaces.
Over my career, I’ve chased foolproof privacy, often settling for approximations. Seismic’s privacy smart contracts Solidity deliver the real deal: native, efficient, Solidity-fluent. Developers, start small, shield strategically, and watch your contracts transform from glass houses to fortresses. The crypto landscape just got a privacy upgrade worth building on.